User Account Control
User Account Control (UAC) is a technology and security infrastructure introduced with Microsoft's Windows Vista, Windows Server 2008 and Windows 7 operating system. It aims to improve the security of Microsoft Windows by limiting application software to standard user privileges until an administrator authorizes an increase or elevation. In this way, only applications trusted by the user may receive administrative privileges, and malware should be kept from compromising the operating system. In other words, a user account may have administrator privileges assigned to it, but applications that the user runs do not inherit those privileges unless they are approved beforehand or the user explicitly authorizes it.
To reduce the possibility of lower-privilege applications communicating with higher-privilege ones, another new technology, User Interface Privilege Isolation is used in conjunction with User Account Control to isolate these processes from each other.[1] One prominent use of this is Internet Explorer 7's "Protected Mode".[2]
Contents |
History
Differentiation of a superuser and userland has been common in mainframes and servers for decades. This had an obvious security component, but also an administrative component, in that it prevented users from accidentally changing system settings.
Microsoft home operating systems (such as MS-DOS, Windows 95, Windows 98 and Windows Me) did not have a concept of different user accounts on the same machine, and all actions were performed as super user. Windows NT introduced multiple user accounts, but in practice most users continued to operate as super user administrator for their normal operations. Further, many applications tend to assume that the user is super user, and will simply not work if he or she is not.[3]
Subsequent versions of Windows and Microsoft applications have encouraged the use of non-administrator user logins, but the uptake has been slow. User Account Control is a stronger approach to do this introduced in Vista. But it is difficult to introduce new security features without breaking existing applications.
When logging into Vista as a standard user, a logon session is created and a token containing only the most basic privileges is assigned. In this way, the new logon session is incapable of making changes that would affect the entire system. When logging in as a user in the Administrators group, two separate tokens are assigned. The first token contains all privileges typically awarded to an administrator, and the second is a restricted token similar to what a standard user would receive. User applications, including the Windows Shell, are then started with the restricted token, resulting in a reduced privilege environment even under an Administrator account. When an application requests higher privileges or "Run as administrator" is clicked, UAC will prompt for confirmation and, if consent is given, start the process using the unrestricted token.[4]
In Windows 7, Microsoft updated UAC in several ways. By default, UAC does not prompt when certain programs included with Windows make changes requiring elevated permissions. Other programs still trigger a UAC prompt. The strictness of UAC can be changed to either always prompt, or to not at all.
Tasks that trigger a UAC prompt
Tasks that require administrator privileges will trigger a UAC prompt (if UAC is enabled); they are typically marked by a 4-color security shield symbol. In the case of executable files, the icon will have a security shield overlay. Ed Bott's Windows Vista Inside Out lists the following tasks which require administrator privileges:[5]
- Running an Application as an Administrator
- Changes to system-wide settings or to files in %SystemRoot% or %ProgramFiles%
- Installing and uninstalling applications
- Installing device drivers
- Installing ActiveX controls
- Changing settings for Windows Firewall
- Changing UAC settings
- Configuring Windows Update
- Adding or removing user accounts
- Changing a user’s account type
- Configuring Parental Controls
- Running Task Scheduler
- Restoring backed-up system files
- Viewing or changing another user’s folders and files
- Running Disk Defragmenter
Common tasks, such as changing the time zone, do not require administrator privileges[6] (although changing the system time itself does, since the system time is commonly used in security protocols such as Kerberos). A number of tasks that required administrator privileges in earlier versions of Windows, such as installing critical Windows updates, no longer do so in Vista.[7] Any program can be run as administrator by right-clicking its icon and clicking "Run as administrator".
Features
User Account Control asks for credentials in a Secure Desktop mode, where the entire screen is temporarily darkened and Windows Aero disabled and only the authorization window is enlightened, to present only the elevation user interface (UI). This is to prevent spoofing of the UI or the mouse by the application requesting elevation.[8] If an administrative activity comes from a minimized application, the secure desktop request will also be minimized so as to prevent the focus from being lost. It is possible to disable Secure Desktop, though this is inadvisable from a security perspective.[9]
Applications written with the assumption that the user will be running with administrator privileges experienced problems in earlier versions of Windows when run from limited user accounts, often because they attempted to write to machine-wide or system directories (such as Program Files) or registry keys (notably HKLM)[3]. UAC attempts to alleviate this using File and Registry Virtualization, which redirects writes (and subsequent reads) to a per-user location within the user’s profile. For example, if an application attempts to write to “C:\program files\appname\settings.ini” and the user doesn’t have permissions to write to that directory, the write will get redirected to “C:\Users\username\AppData\Local\VirtualStore\Program Files\appname\settings.ini”.
There are a number of configurable UAC settings. It is possible to:[10]
- Require administrators to re-enter their password for heightened security;
- Require the user to press Ctrl+Alt+Del as part of the authentication process for heightened security;
- Disable Admin Approval Mode (UAC prompts for administrators) entirely;
Command Prompt windows that are running elevated will prefix the title of the window with the word "Administrator", so that a user can discern which instances are running with elevated privileges.[11]
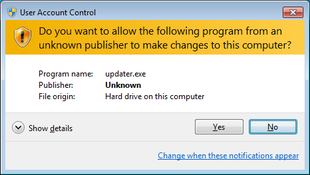
A distinction is made between elevation requests from a signed executable and an unsigned executable; and if the former, whether the publisher is 'Windows Vista'. The color, icon, and wording of the prompts are different in each case; for example, attempting to convey a greater sense of warning if the executable is unsigned than if not.[12]
Internet Explorer 7's "Protected Mode" feature uses UAC to run with a 'low' integrity level (a Standard user token has an integrity level of 'medium'; an elevated (Administrator) token has an integrity level of 'high'). As such, it effectively runs in a sandbox, unable to write to most of the system (apart from the Temporary Internet Files folder) without elevating via UAC.[4][13] Since toolbars and ActiveX controls run within the Internet Explorer process, they will run with low privileges as well, and will be severely limited in what damage they can do to the system.[14]
Requesting elevation
A program can request elevation in a number of different ways. One way for program developers is to add a requestedPrivileges section to an XML document, known as the manifest, that is then embedded into the application. A manifest can specify dependencies, visual styles, and now the appropriate security context:
<?xml version="1.0" encoding="UTF-8" standalone="yes"?> <assembly xmlns="urn:schemas-microsoft-com:asm.v1" manifestVersion="1.0"> <v3:trustInfo xmlns:v3="urn:schemas-microsoft-com:asm.v3"> <v3:security> <v3:requestedPrivileges> <v3:requestedExecutionLevel level="highestAvailable"/> </v3:requestedPrivileges> </v3:security> </v3:trustInfo> </assembly>
Setting the level attribute for requestedExecutionLevel to "asInvoker" will make the application run with the token that started it, "highestAvailable" will present a UAC prompt for administrators and run with the usual reduced privileges for standard users, and "requireAdministrator" will require elevation.[15] In both highestAvailable and requireAdministrator modes, failure to provide confirmation results in the program not being launched.
An executable that is marked as "requireAdministrator" in its manifest cannot be started from a non-elevated process using CreateProcess(). Instead, ERROR_ELEVATION_REQUIRED will be returned. ShellExecute() or ShellExecuteEx() must be used instead. If an HWND is not supplied, then the dialog will show up as a blinking item in the taskbar.
Inspecting an executable's manifest to determine if it requires elevation is not recommended, as elevation may be required for other reasons (setup executables, application compatibility). However, it is possible to programmatically detect if an executable will require elevation by using CreateProcess() and setting the dwCreationFlags parameter to CREATE_SUSPENDED. If elevation is required, then ERROR_ELEVATION_REQUIRED will be returned.[16] If elevation is not required, a success return code will be returned at which point you can use TerminateProcess() on the newly created, suspended process. This will not allow you to detect that an executable requires elevation if you are already executing in an elevated process, however.
A new process with elevated privileges can be spawned from within a .NET application using the "runas" verb. An example using C++/CLI:
System::Diagnostics::Process^ proc = gcnew System::Diagnostics::Process(); proc->StartInfo->FileName = "C:\\Windows\\system32\\notepad.exe"; proc->StartInfo->Verb = "runas"; // Elevate the application proc->Start();
In a native Win32 application the same "runas" verb can be added to a ShellExecute() or ShellExecuteEx() call.[4]
ShellExecute(hwnd, "runas", "C:\\Windows\\Notepad.exe", 0, 0, SW_SHOWNORMAL);
In the absence of a specific directive stating what privileges the application requests, UAC will apply heuristics, to determine whether or not the application needs administrator privileges. For example, if UAC detects that the application is a setup program, from clues such as the filename, versioning fields, or the presence of certain sequences of bytes within the executable, in the absence of a manifest it will assume that the application needs administrator privileges.[17]
Criticism
There have been complaints that UAC notifications slow down various tasks on the computer such as the initial installation of software onto Windows Vista.[18] It is possible to turn off UAC while installing software, and reenable it at a later time.[19] However, this is not recommended since, as File & Registry Virtualization is only active when UAC is turned on, user settings and configuration files may be installed to a different place (a system directory rather than a user-specific directory) if UAC is switched off than they would be otherwise.[20] Also note that Internet Explorer 7's "Protected Mode", whereby the browser runs in a sandbox with lower privileges than the standard user, relies on UAC; and will not function if UAC is disabled.[13]
Yankee Group analyst Andrew Jaquith stated that "while the new security system shows promise, it is far too chatty and annoying."[21] However, this statement was made over six months before Vista was actually released (even before Beta 2 was released). By the time Windows Vista was released in November 2006, Microsoft had drastically reduced the number of operating system tasks that triggered UAC prompts, and added file and registry virtualization to reduce the number of legacy applications that trigger UAC prompts.[3] However, David Cross, a product unit manager at Microsoft, stated during the RSA Conference 2008 that UAC was in fact designed to "annoy users," and force independent software vendors to make their programs more secure so that UAC prompts would not be triggered.[22] In response to these criticisms, Microsoft has altered UAC activity in Windows 7. For example, by default users are not prompted to confirm actions initiated with the mouse and keyboard alone such as operating Control Panel applets. New York Times Gadgetwise writer Stephen Williams says: "One recommended way to wring more speed from Vista is to turn off the overly protective User Account Control whose pop-ups are like having your mother hover over your shoulder while you work."[23]. A study by Sophos using 10 unique samples which had arrived in their labs, showed that UAC , on its default level, could not protect Windows 7 from 8 of the samples. [24]
See also
- Comparison of privilege authorization features
- Features new to Windows Vista
- Least user access (LUA)
- runas
- Security and safety features of Windows Vista
References
- ↑ "The Windows Vista and Windows Server 2008 Developer Story: Windows Vista Application Development Requirements for User Account Control (UAC)". The Windows Vista and Windows Server 2008 Developer Story Series. Microsoft. April 2007. http://msdn2.microsoft.com/en-us/library/aa905330.aspx. Retrieved 2007-10-08.
- ↑ "Understanding and Working in Protected Mode Internet Explorer". Microsoft. January 2006. http://msdn2.microsoft.com/en-us/library/bb250462.aspx. Retrieved 2007-12-08.
- ↑ 3.0 3.1 3.2 Torre, Charles (March 5, 2007). "UAC - What. How. Why." (video). http://channel9.msdn.com/ShowPost.aspx?PostID=288259. Retrieved 2007-12-08.
- ↑ 4.0 4.1 4.2 Kerr, Kenny (September 29, 2006). "Windows Vista for Developers – Part 4 – User Account Control". http://weblogs.asp.net/kennykerr/archive/2006/09/29/Windows-Vista-for-Developers-_1320_-Part-4-_1320_-User-Account-Control.aspx. Retrieved 2007-03-15.
- ↑ Bott, Ed (2007-02-02). "What triggers User Account Control prompts?". http://www.edbott.com/weblog/?p=1602.
- ↑ Allchin, Jim (2007-01-23). "Security Features vs. Convenience". Windows Vista Team Blog. Microsoft. http://windowsvistablog.com/blogs/windowsvista/archive/2007/01/23/security-features-vs-convenience.aspx. Retrieved 2007-03-04.
- ↑ "User Account Control Overview". Technet. Microsoft. http://technet.microsoft.com/en-us/windowsvista/aa906021.aspx.
- ↑ "User Account Control Prompts on the Secure Desktop". UACBlog. MSDN Blogs. 2006-05-03. http://blogs.msdn.com/uac/archive/2006/05/03/589561.aspx. Retrieved 2007-02-25.
- ↑ Bott, Ed (February 2, 2007). "Why you need to be discriminating with those Vista tips". Ed Bott's Windows Expertise. http://www.edbott.com/weblog/?p=1600. Retrieved 2007-12-08.
- ↑ "Chapter 2: Defend Against Malware". Windows Vista Security Guide. Microsoft. November 8, 2006. http://technet.microsoft.com/en-us/bb629436.aspx. Retrieved 2007-03-15.
- ↑ "Administrator Marking for Command Prompt". UACBlog. MSDN Blogs. August 1, 2006. http://blogs.msdn.com/uac/archive/2006/08/01/685645.aspx. Retrieved 2006-08-07.
- ↑ "Accessible UAC Prompts". Windows Vista Blog. Microsoft. http://windowsvistablog.com/blogs/windowsvista/archive/2007/01/25/accessible-uac-prompts.aspx.
- ↑ 13.0 13.1 Russinovich, Mark (June 2007). "Inside Windows Vista User Account Control". TechNet Magazine. Microsoft. http://www.microsoft.com/technet/technetmag/issues/2007/06/UAC/. Retrieved 2007-12-08.
- ↑ Friedman, Mike. "Protected Mode in Vista IE7". IEBlog. http://blogs.msdn.com/ie/archive/2006/02/09/528963.aspx.
- ↑ Mike Carlisle (2007-03-10). "Making Your Application UAC Aware". The Code Project. http://www.codeproject.com/KB/vista-security/MakingAppsUACAware.aspx. Retrieved 2007-03-15.
- ↑ Junfeng Zhang (2006-10-18). "Programmatically determine if an application requires elevation in Windows Vista". MSDN Blogs. http://blogs.msdn.com/junfeng/archive/2006/10/18/programmatically-determine-if-an-application-requires-elevation-in-windows-vista.aspx. Retrieved 2008-01-24.
- ↑ "Understanding and Configuring User Account Control in Windows Vista". Microsoft. http://technet2.microsoft.com/WindowsVista/en/library/00d04415-2b2f-422c-b70e-b18ff918c2811033.mspx?mfr=true. Retrieved 2007-07-05.
- ↑ "Disabling the UAC feature". 2007-03-10. http://lifehacker.com/software/vista/geek-to-live-windows-vista-upgrade-power-tips-231922.php. Retrieved 2007-03-10.
- ↑ "Disable UAC in Vista". http://www.youtube.com/watch?v=M7Uwx_yaxUM.
- ↑ Bott, Ed (2007-02-02). "Why you need to be discriminating with those Vista tips". Ed Bott's Windows Expertise. http://www.edbott.com/weblog/?p=1600. Retrieved 2007-07-05.
- ↑ Evers, Joris (2006-05-07). "Report: Vista to hit anti-spyware, firewall markets". ZDNet News. CNet. http://news.zdnet.com/2100-1009_22-6069464.html. Retrieved 2007-01-21.
- ↑ Microsoft: Vista feature designed to 'annoy users' | Tech News on ZDNet
- ↑ Gadgetwise, New York Times, May 14, 2008.
- ↑ http://www.sophos.com/blogs/chetw/g/2009/11/03/windows-7-vulnerable-8-10-viruses/
External links
- Documentation about UAC for Windows 7, Windows Server 2008, Windows Server 2008 R2, Windows Vista
- Information at Windows Vista Forums
- UAC Understanding and Configuring More Information at Microsoft Technet
- Development Requirements for User Account Control Compatibility More information at Microsoft Developer Network
- UAC Team Blog
- UAC–The Good and The Bad Joanna Rutkowska
- Security Features vs. Convenience
|
|||||||||||||||||||||||||||||||||||